What is Phishing Email?
A phishing email, dispatched by cyber criminals, is a deceptive message designed to obtain money or sensitive information. The term “phishing” is a spin on the word “fishing”, metaphorically hinting at the deceptive tactics such as fake email addresses, bogus websites, and fabricated security certificates to lure unsuspecting victims.
Modern malicious emails can be extremely convincing and difficult to recognize. Hence, it's crucial for every email user to learn how to spot a phishing email and master strategies to thwart such cyber attacks.
How to Prevent Phishing Attacks?
Phishing attacks have been around for several decades, and they have evolved dramatically over the years. Many tips on how to stop and prevent a phishing attack in Gmail and other email providers have become outdated, while other tips are still relevant to this day.
1. Be Wary of Unknown Senders
Be highly cautious when receiving personal emails from unknown senders. Phishers often impersonate genuine businesses and individuals to steal login credentials and other personal data. Their success relies on your deceived actions.
Upon receiving a suspicious request for personal information, it's important to act. Don’t hesitate to contact the sender or run a reverse email search before replying.
IT administrators sometimes like to simulate a phishing attack because they want to teach employees that email addresses can be faked, and you don’t want to label yourself as someone who blindly trusts emails from unknown senders.
2. Look for Bad Grammar and Improper Spelling
Long gone are the days of Nigerian princes asking for small loans in exchange for millions of dollars, but emails with bad grammar and improper spelling are still very common among other phishing techniques. You may even stumble upon a phishing email written in completely broken English that’s below the level of leading machine translation tools.
In a more devious twist, cybercriminals sometimes employ subtle misspellings to deceive their victims. For example, replacing "Apple" (lowercase L) with "AppIe" (capital I) allows them to register a fake domain that's visually identical to the real one. This trick is often used to mislead users into clicking fraudulent links, which then capture personal data or facilitate financial theft. Keep in mind that domain names, email addresses, and even URLs can be faked using this tactic to ensnare unsuspecting victims.
3. Avoid Suspicious Attachments
Legitimate organizations rarely use email attachments, unlike phishers. In a typical Apple phishing scam, cybercriminals distribute fake invoices, mimicking real ones. These can contain malware or fake links to fraudulent sites, identical to Apple's genuine website.
As declared by cybersecurity powerhouse Trend Micro, these fraudulent sites are designed to pilfer login credentials, effectively giving scammers access to the accounts of unwary Apple users. It's thus essential to verify the legitimacy of email attachments and the websites they link to, underlining the importance of vigilance in online communications.
4. Learn to Recognize Common Types of Phishing Scams
There are at least eight common email phishing campaign types that you should learn to recognize:
- Deceptive Phishing: This prevalent type involves cybercriminals posing as legitimate entities through emails, aiming to trick recipients into divulging sensitive data. This tactic often uses email spoofing to appear more credible.
- Spear Phishing: This is a more personalized version of deceptive phishing. Cybercriminals tailor their attacks with specific details about the victim, making their deceptive requests appear more plausible.
- CEO Fraud/Business Email Compromise (BEC): This scam involves impersonating company executives to exploit their authority. The aim is to trick employees into authorizing fraudulent financial transactions.
- Pharming: In this method, attackers hijack a website’s domain and redirect it to a false site. Users, thinking they're on a trusted site, inadvertently provide sensitive information to the phishers.
- Cloud Storage Phishing: This broad category includes phishing attempts mimicking popular cloud services such as Dropbox, Google Docs, OneDrive, iCloud, and others. Attackers send realistic-looking emails to users prompting them to click a link to secure their account or access a shared document. This link then leads to deceptive sites designed to steal their credentials.
- Smishing and Vishing: These are phishing variants that use fraudulent text messages (Smishing) or voice calls (Vishing) instead of emails to deceive victims.
- Watering Hole Phishing: In this method, attackers infect a site frequented by their targets. When the targets visit the compromised site, their devices get infected with malicious software.
- HTTPS Phishing: In this method, attackers exploit users' trust in the 'https' prefix by creating fraudulent URLs with it, thus creating a false sense of security.
Looking for more information about email security to keep your company messages safe and protected? Check out our article about email security best practices and follow our guide on how to send a secure email in Gmail, Outlook, Yahoo, and other private email providers. Learn how to avoid AT&T spam emails and phishing scams.
5. Keep Your Inbox Clean and Organized
Phishing emails thrive on messy, crowded inboxes — a problem many of us face when bombarded with countless messages every day. But managing your inbox can be made simpler and more doable with Clean Email, a powerful email cleaner tool designed to help keep things tidy. Stay tuned for the next chapter where we'll dive deeper into how Clean Email works.
Put an End to Email Phishing with Clean Email
Clean Email, a comprehensive email management app, provides a line of defense against phishing and spam with features like the Screener and Privacy Monitor. Furthermore, its automation capabilities, including Auto Clean and Unsubscriber, help maintain an organized and spam-free inbox.
It’s available on the web, iOS, and Android, so you can keep your inbox clean on any device.
The Screener feature in Clean Email clusters similar emails for expedited review, significantly minimizing the risk of phishing attacks. By allowing users to quickly identify and isolate suspicious emails, it offers a proactive approach to maintaining a secure and spam-free inbox.
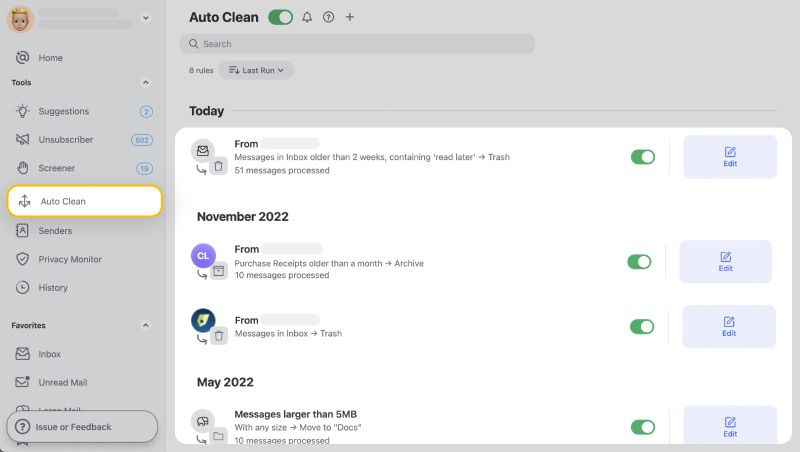
The Auto Clean feature enables you to set up automated rules for handling incoming emails from selected senders or domains. Additionally, you can customize these rules with extra filters and criteria to enhance your email management. You can effortlessly manage your rules from a user-friendly dashboard, streamlining your email workflow.
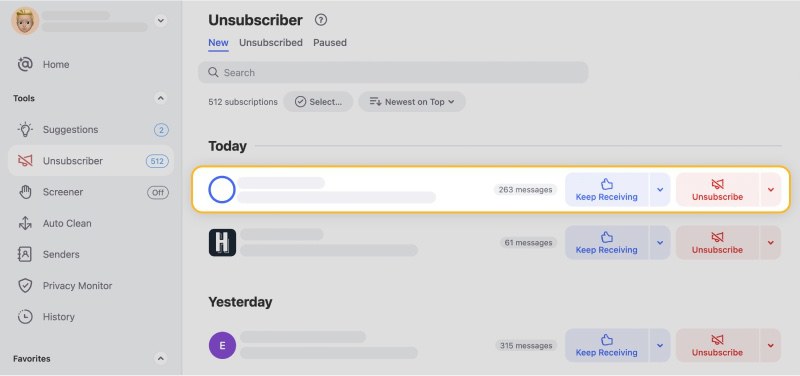
Unsubscriber is perfect for unsubscribing from unwanted marketing emails, which may actually be phishing emails in disguise. Even if the sender does not provide an option to unsubscribe, Clean Email will make sure that unwanted emails won't stay in your inbox and bring your productivity to a screeching stop.
Phishing schemes are increasingly sophisticated, becoming more personalized and convincingly authentic. The number and variety of these attacks can be genuinely daunting, heightening the risk of unsuspecting users falling into these carefully crafted traps. In this context, Clean Email's Privacy Monitor serves as a vital line of defense, routinely scanning for your email in any known data breaches.
Privacy Monitor diligently scans for your email address within known data breaches, serving as a defensive barrier against the potential fallout from inadvertent clicks on malicious emails. If your account is detected in a data breach, Privacy Monitor promptly alerts you, recommending a password change. This proactively shields you from severe repercussions, keeping your online communications secure and controlled even in the face of potential phishing threats.
Conclusion
In the digital age, phishing attacks continue to pose a significant risk to individuals and businesses alike. Yet, armed with knowledge and effective tools like Clean Email, users can better safeguard their inboxes from these cyber threats. Remember, maintaining a clean and organized inbox is not just a matter of convenience, but a vital step towards enhanced online security.
How to Avoid Phishing Attacks - FAQs
What is a phishing email?
A phishing email is a fraudulent message aimed at obtaining sensitive information, like login or financial details. They mimic legitimate entities, using deceptive links and websites to fool recipients.
What happens if you open a phishing email?
The consequences of opening a phishing email depend on the goal of the phisher. Clicking on a link, attachment, or even opening a phishing message can start installing malware, such as viruses, spyware, or ransomware, onto your device.
Where do I report phishing emails?
Phishing emails can be reported to the Anti-Phishing Working Group at reportphishing@apwg.org. Alternatively, you can report them to the Federal Trade Commission (FTC) at ftc.gov/complaint or forward them to the FTC's spam reporting address: spam@uce.gov.
What are examples of phishing scams?
Phishing examples include deceptive phishing (impersonating legitimate entities), spear phishing (personalized deceptive emails), CEO Fraud/Business Email Compromise (impersonating company executives), pharming (redirecting to fraudulent sites), cloud storage phishing (mimicking cloud services), and Smishing/Vishing (using fraudulent text messages or voice calls).
What do I do if I responded to a phishing email?
If you respond to a phishing email, you need to change your account’s password immediately. If your online banking account or any other personal account has the same password, change it too. Also, you should call your bank for good measure and make them aware that there was a security breach incident. Depending on your bank protocols, they might issue you a new account number. After you have secured your most vulnerable accounts, go back to your email and ensure that you have good anti-spam software and the latest edition of your internet browser installed.
How do I get rid of phishing emails?
To get rid of phishing emails, it is essential to stay vigilant and cautious. Mark suspicious emails as spam, avoid clicking on any suspicious links or attachments, and regularly update your email security settings. Wisely use security tools and install reliable anti-spam and anti-virus software to enhance your phishing protection. Additionally, consider using email management tools like Clean Email, which can help declutter your inbox and reduce the chances of receiving phishing emails.


