What is Email Spoofing?
Email spoofing is a type of cyberattack where someone sends a message that looks like it’s from a trusted source, but the sender’s address has been faked. It's relatively common and effective because most people don’t check the small details (like the display name or domain address) that can reveal something’s off with the email.
SMTP (the email protocol) doesn’t automatically verify sender identity by itself, so attackers can forge From: headers. Thankfully, many mail providers and servers run automatic checks using SPF, DKIM, and DMARC, and most email clients (Gmail, Outlook, Yahoo, etc.) make those authentication results visible to users.
📌 While email spoofing has some similarities to account hacking, the two attacks have different goals. Email spoofing disguises an email’s From: address without accessing the account, while account hacking involves gaining unauthorized access to the inbox.
What Does Email Spoofing Look Like?
A spoofed email changes the metadata of the email (usually the sender field) to make the email seem more genuine. Attackers commonly do this in three ways:
Display-name spoofing
This is when the attacker sets the display name to something familiar (for example, “PayPal Support” or “Company HR”) while the actual sending address (for example, “support@paypalattack.com” instead of “support@paypal.com”) is different.
This works because email headers contain both a human-readable name and an email address (From: "PayPal Support" <fraudster@example.com>). Many mail clients show the display name prominently and hide the real email by default, which makes spoofed emails look more convincing at first glance.
Domain spoofing
Someone sends an email that looks like it came from a real domain you trust (for example, boss@yourcompany.com), but it didn’t come from your company at all. It takes advantage of a simple but powerful assumption: that emails from familiar domains are automatically trustworthy.
Attackers set the From: header to the domain name they’re trying to impersonate. Because an SMTP server does not inherently verify the sender’s identity, a forged address may appear legitimate unless SPF, DKIM, or DMARC checks are enforced.
Lookalike or impersonation
In this type of spoofing, an attacker sends an email from a domain that visually resembles a legitimate domain (for example: paypa1.com with the digit 1 or rnicrosoft.com vs microsoft.com).
They may also use subdomain tricks like account.paypal.com.attacker.com, which can sometimes just appear as account.paypal.com.
This method works because most people don’t really examine domain names that closely—and if they do, attackers can simply choose to replace or add characters that look nearly identical.
How a more organized inbox can protect you against email spoofing
An organized inbox doesn't directly prevent spoofed emails, but it allows you to more easily spot and filter them. Using filters and labels, you can separate legitimate emails from spam and suspicious messages while training your email client to recognize unusual patterns over time.
This process complements stronger, technical defenses like using email authentication protocols (SPF, DKIM, and DMARC) and using secure email providers and services.
Most spoofed messages succeed because users overlook them in the chaos of newsletters, spam, and unread emails. Secure services like Clean Email help reduce that clutter, automatically filter messages from unknown senders, and keep legitimate messages visible, making it much harder for spoofed messages to slip through.
Some Clean Email benefits that can help you avoid email spoofing include:
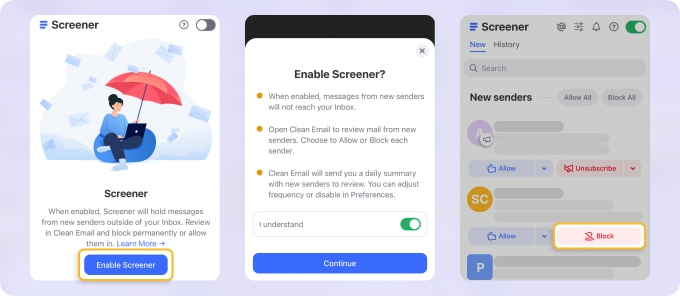
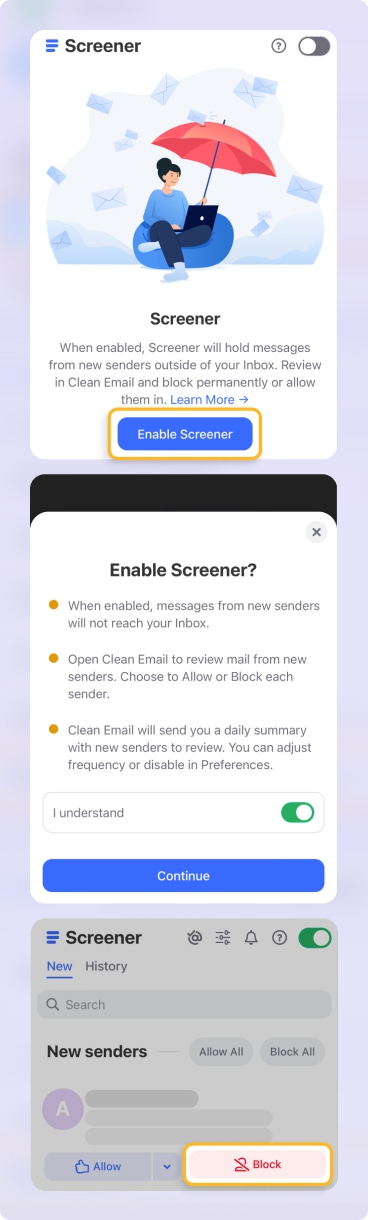
- Screener: Keeps messages from unknown senders separate until approved by you, stopping spoofed or phishing attempts before they enter the inbox.
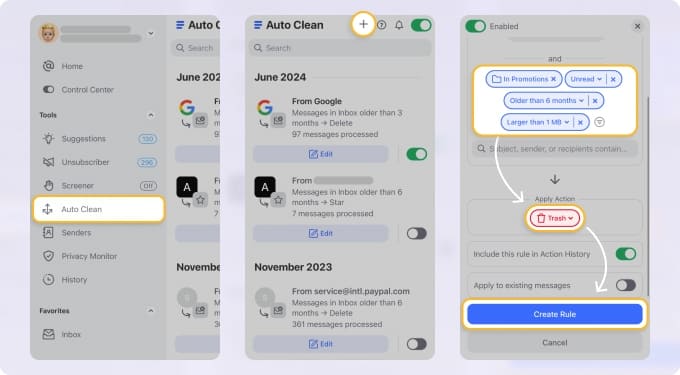
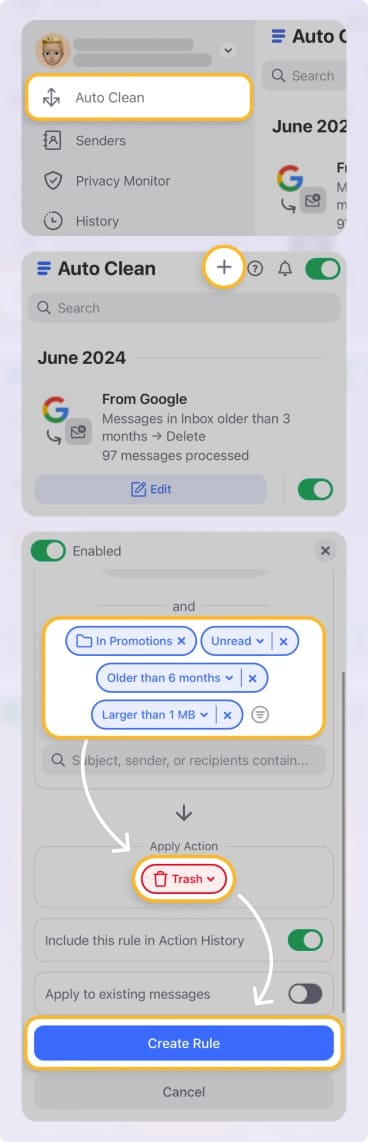
- Automatic Filtering with Auto Clean Rules: Organizes and filters emails so spoofed messages stand out instead of hiding among clutter.
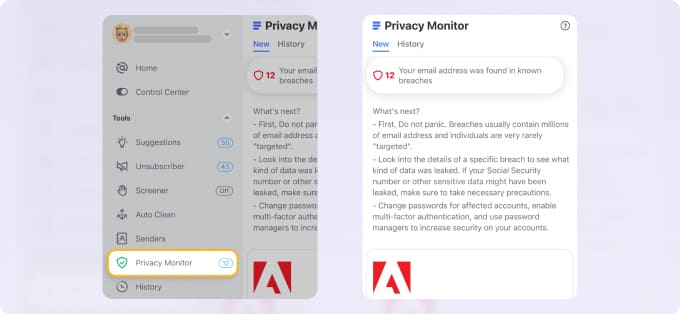
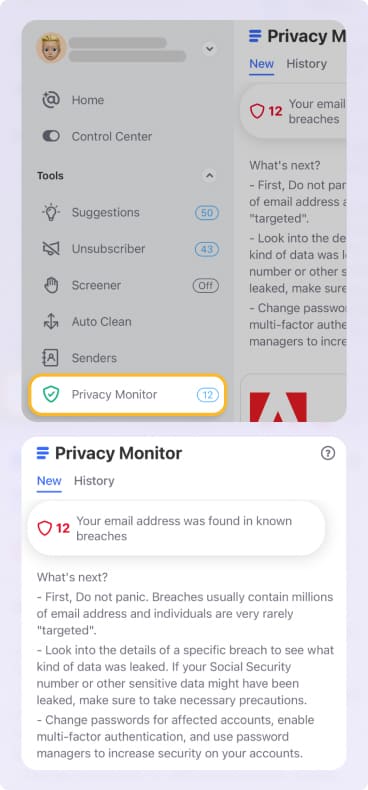
- Privacy Monitor: Works in the background and notifies you if there’s a data leak and your email credentials were compromised.
- Privacy Protection: Clean Email never reads or sells your data—its algorithms work locally to protect privacy while maintaining order.
An organized inbox is easier to manage, and Clean Email can automate much of this process. This gives you a hassle-free inbox where potential spoofed emails are easier to spot.
Email Spoofing Prevention: Why SPF, DKIM, and DMARC Matter
SPF (Sender Policy Framework), DKIM (DomainKeys Identified Mail), and DMARC (Domain-based Message Authentication, Reporting, and Conformance) are email authentication protocols that work together to verify a sender's identity. They help form a strong defense against email phishing, spoofing, and other email-based attacks.
- SPF verifies that an email comes from an authorized IP address.
- DKIM adds a digital signature to verify the sender and ensure the message hasn't been tampered with.
- DMARC uses both SPF and DKIM to tell the recipient's server what action to take when a message fails authentication.
SPF or DKIM failures aren’t always signs of an attack. Legitimate forwarding, mailing lists, or misconfigured third-party senders can also cause failures. That’s why DMARC alignment and monitoring of DMARC reports are important before enabling actions like quarantine/reject.
So if you’re wondering how to stop spammers from spoofing your email, SPF, DKIM, and DMARC are often your first line of defense. They provide email spoofing protection through authorization, integrity, and enforcement.
Additionally, using a bulk email verification tool can help ensure that the emails in your list are valid and active, reducing the chance of spam complaints or spoofing risks.
How to Stop Email Spoofing by Enabling SPF, DKIM, and DMARC
The key anti-spoofing actions you can take for your domain are enabling SPF, DKIM, and DMARC. These protocols are not enabled by default on all email clients; they must be configured by the domain owner. They’re added as DNS records, and they work at the domain level to reduce spam, prevent email spoofing, and protect against related threats like DNS spoofing.
While many email providers like Google now enforce stricter requirements and may handle some basic setup, full and accurate configuration is still the domain owner's responsibility.
Below are the steps for enabling these protections on some of the most commonly used email clients. Before making any changes, always back up current DNS records and allow time for DNS propagation for up to 24-48 hours.
How to stop email spoofing in Gmail for business (Google Workspace)
SPF
- Sign in to your DNS host (where your domain’s records live).
- Create or edit a TXT record with:
Name/Host: @
Value: v=spf1 include:_spf.google.com ~all - Make sure you only have one SPF TXT record for the domain since multiple records can cause authentication failures.
DKIM
- In Google Admin console: Apps → Google Workspace → Gmail → Authenticate email.
- Generate a new DKIM key (choose 2048-bit if available).
- Copy the host name and the value Google provides. Add them as a TXT record in your DNS.
- After DNS propagation, return to the Admin console and click Start authentication.
DMARC
- Wait until SPF and DKIM have been active for at least ~48 hours.
- In your DNS host, add a TXT record:
Name/Host: _dmarc.yourdomainname.com
Value: v=DMARC1; p=none; rua=mailto:reports@yourdomain.com
(Then later you can change p= to quarantine or reject) - Monitor the reports you receive and once you’re confident your legitimate email traffic is properly authenticated, move to a stricter policy.
How to stop email spoofing in Office 365
SPF
- At your DNS host, add a TXT record:
Name/Host: @
Value: v=spf1 include:spf.protection.outlook.com -all - Proceed to configure your DKIM.
DKIM
- In Microsoft 365 Admin Center → Exchange → Protection → DKIM.
Alternatively, you can also do this via PowerShell: Connect-ExchangeOnline and Set-DkimSigningConfig for your domain. - Before enabling, publish two CNAME records in your DNS:
Name/Host: selector1._domainkey.yourdomain.com → Value: selector1-yourdomain-com._domainkey.yourdomain.onmicrosoft.com
Name/Host: selector2._domainkey.yourdomain.com → Value: selector2-yourdomain-com._domainkey.yourdomain.onmicrosoft.com - After DNS has propagated, enable DKIM for your domain in the portal.
DMARC
- At your DNS host, add a TXT record:
Name/Host: _dmarc
Value: v=DMARC1; p=none; rua=mailto:you@yourdomain.com - You can change p= to quarantine or reject once you're sure all legitimate sending sources are covered.
How to stop email spoofing in cPanel
SPF & DKIM
- Log in to cPanel.
- Go to Email → Email Deliverability.
For SPF: install the suggested record or customize it.
For DKIM: click Install the suggested record under DKIM. - On WHM (for server admins), enable DKIM/SPF globally:
WHM → Home → DNS Functions → Enable DKIM/SPF Globally.
DMARC
- In cPanel, go to Zone Editor (Domains section). Add a TXT record:
Name/Host: _dmarc.yourdomain.com
Type: TXT
Value: v=DMARC1; p=quarantine; rua=mailto:you@yourdomain.com - Start with p=none for monitoring, then change to quarantine or reject if needed.
How to stop email spoofing in GoDaddy
SPF
- In your GoDaddy dashboard → Domain Portfolio → DNS.
- Add a TXT record:
Host: @
Value: v=spf1 include:secureserver.net -all
DKIM
- If using GoDaddy hosting (cPanel/VPS):
Go to cPanel → Email Deliverability → Manage → get the suggested DKIM name & value. Add them as a TXT record in your GoDaddy DNS.
- For Microsoft 365:
Add the DKIM CNAME records provided by Microsoft.
DMARC
- In GoDaddy’s DNS manager, add a TXT record:
Name: _dmarc
Value: v=DMARC1; p=none; adkim=r; aspf=r; rua=mailto:dmarc_rua@onsecureserver.net - p can be left at quarantine first, but you may set it to none or reject as needed.
Always enable SPF first, so you declare which servers can send emails for your domain, then enable DKIM so your outgoing mail gets cryptographically signed.
Only after enabling SPF and DKIM should you add DMARC, so you specify how receivers should treat emails that fail SPF/DKIM checks and start receiving reports.
How to Check for Email Spoofing
You can also manually check messages for signs of spoofing. While this can take time, it’s a straightforward way to determine whether an email is potentially malicious.
Gmail
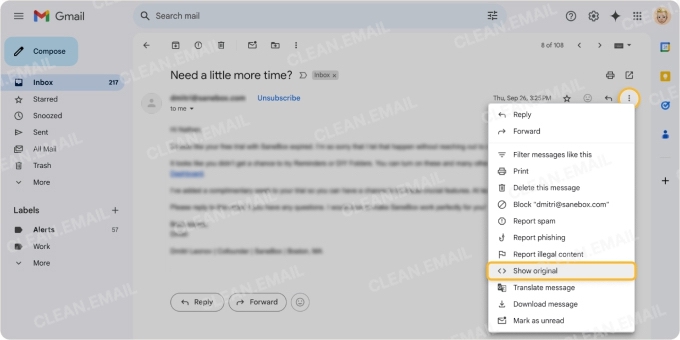
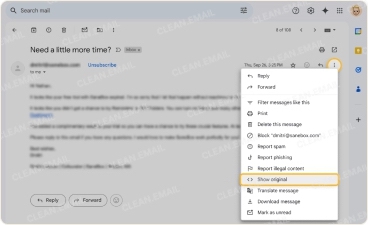
- Open the email → click the three-dot menu → click Show original.
- In the header, check the Authentication-Results section. If you see something like spf=fail or dkim=fail for the domain in the From: header, there’s a strong likelihood that the email may be spoofed.
- Check that the domain in the From: header matches the domains in the Return-Path or Received: lines. If they don’t align, the email may be spoofed.
Outlook
- In Outlook desktop: open the message → File → Properties → look under Internet headers.
- In Outlook.com: open message → click three-dots menu → View message source.
- Look for the Authentication-Results: header. If SPF/DKIM shows that it failed (or is missing) for the domain in the From: header, the email could be spoofed.
- Check the Received: header chain. The bottom entry (or the earliest hop) should come from a legitimate server for the sender’s domain. If it isn’t, you may be dealing with a spoofed email.
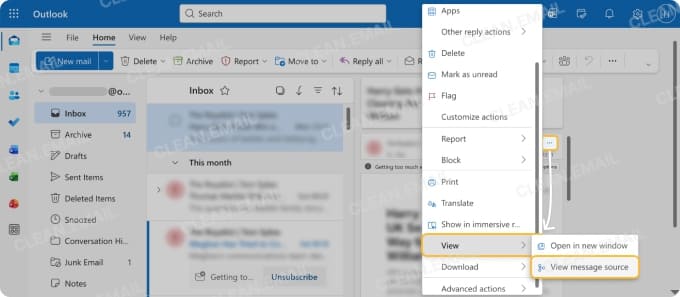
Following these checks can help you identify suspicious messages and take action, a key part of how to stop email spoofing in Outlook.
Yahoo Mail
- Open the email → click the three-dot menu → View raw message.
- Scroll to the Authentication-Results and check SPF/DKIM. If they’re absent or show fail, treat the email as spoofed.
- Confirm that the domain in the From: header matches the domain used in SPF/DKIM/DMARC. If it doesn’t, the email may be spoofed.


By following these steps, you can verify senders and protect your account, which is key to stopping email spoofing in Yahoo.
Practical User-Level Security Tips
Users also play a crucial role in stopping spoofed emails from reaching their email addresses. Follow these best practices:
- Inspect email headers for unusual sender addresses/domains.
- Report suspicious emails to your IT team or email provider immediately.
- Enable multi-factor authentication for an extra layer of security.
- Avoid clicking links or downloading attachments from unknown/unexpected senders.
Don’t Get Fooled by Appearances
Email spoofing can’t be fully eliminated, but organized inbox management and authentication drastically reduce the risks. By enabling SPF/DKIM/DMARC, you give mail servers the tools needed to verify senders and reject spoofed emails.
How to Stop and Prevent Email Spoofing – FAQs
Has my account been hacked?
Not necessarily. Spoofing fakes your address without accessing your inbox. If nothing in your account looks unusual, your account is still secure.
What to do if my email was spoofed?
Let your contacts know to ignore the fake messages and confirm your account hasn’t been accessed. Then set up SPF, DKIM, and DMARC so future spoofed emails are rejected. Continue monitoring for anything suspicious.
Can I stop someone from spoofing my address?
You can’t stop attackers from trying, but you can make their emails fail authentication. SPF, DKIM, and DMARC tell receiving servers which messages are truly from you. With these in place, spoofed emails are far less likely to reach anyone.
How to stop spoofing emails from my email address?
Set up SPF and DKIM first, then enable DMARC to instruct mail servers how to handle forged messages. Make sure any service that sends mail on your behalf is properly included in these records. Once everything aligns, most spoofed messages are blocked automatically.


